Self-securing Networks
Status
This project started in 2019 and has been successfully completed in 2022.
Researchers
Albert Gran Alcoz (ETH)
Laurent Vanbever (ETH)
Martin Strohmeier (Armasuisse)
Vincent Lenders (Armasuisse)
Industry partner
armasuisse
Description
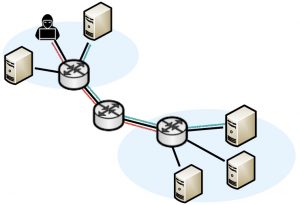
The goal of this project is to build data-driven network infrastructures that can autonomously protect, detect and defend themselves against attacks. We intend to develop network-specific learning and inference algorithms that can run directly in the data plane, in real-time, to perform tasks that are difficult to solve today such as (encrypted) traffic classification and fine-grained anomaly detection. To implement these learning and inference algorithms, we intend to leverage the newly available capabilities of programmable data planes to run complex forwarding logics. Specifically, we will use these capabilities to: (i) extract representative network data; (ii) train learning models; and (iii) drive forwarding decisions accordingly— at line rate.
Traffic classification: In a first package, we intend to build in-network online classification mechanisms. Traffic classification is a key building block when securing today’s networks. Classifying traffic directly in the network enables network devices to adapt their forwarding decisions according to the application types. For instance, it enables network switches to direct specific flows to dedicated boxes for further processing. It also enables switches to drop traffic (or possibly de-prioritize it) as soon as it enters the network.
Anomaly detection: In a second package, we intend to investigate methods and tools on top of programmable data planes to perform anomaly detection network-wide, ideally on all the traffic. While performing large-scale anomaly detection is highly challenging and requires fundamental research contributions, one can use simpler, detection mechanisms in the data plane, and compensate for their lack of precision (i.e.. false positives) with lightweight confirmation stages.
Data-driven defenses: In a third package, we intend to consider the problem of active, data-driven network defenses. Intuitively, while the two first packages consider the problem of sensing the network, this work package will consider the problem of actuating the network accordingly, i.e. closing the control loop. Here we plan on developing several techniques to confirm and mitigate alleged attacks.
Publications
Albert Gran Alcoz, Martin Strohmeier, Vincent Lenders, Laurent Vanbever.
Aggregate-Based Congestion Control for Pulse-Wave DDoS Defense.
ACM SIGCOMM 2022. Amsterdam, Netherlands (August 2022).
[PDF]
